Understanding IDS/IPS
What are IDS and IPS?
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are cybersecurity technologies designed to monitor network traffic for signs of malicious activity.
- IDS: Monitors network traffic and alerts security teams when suspicious activities are detected.
- IPS: Not only detects suspicious activities but also takes action to prevent potential threats from causing harm.
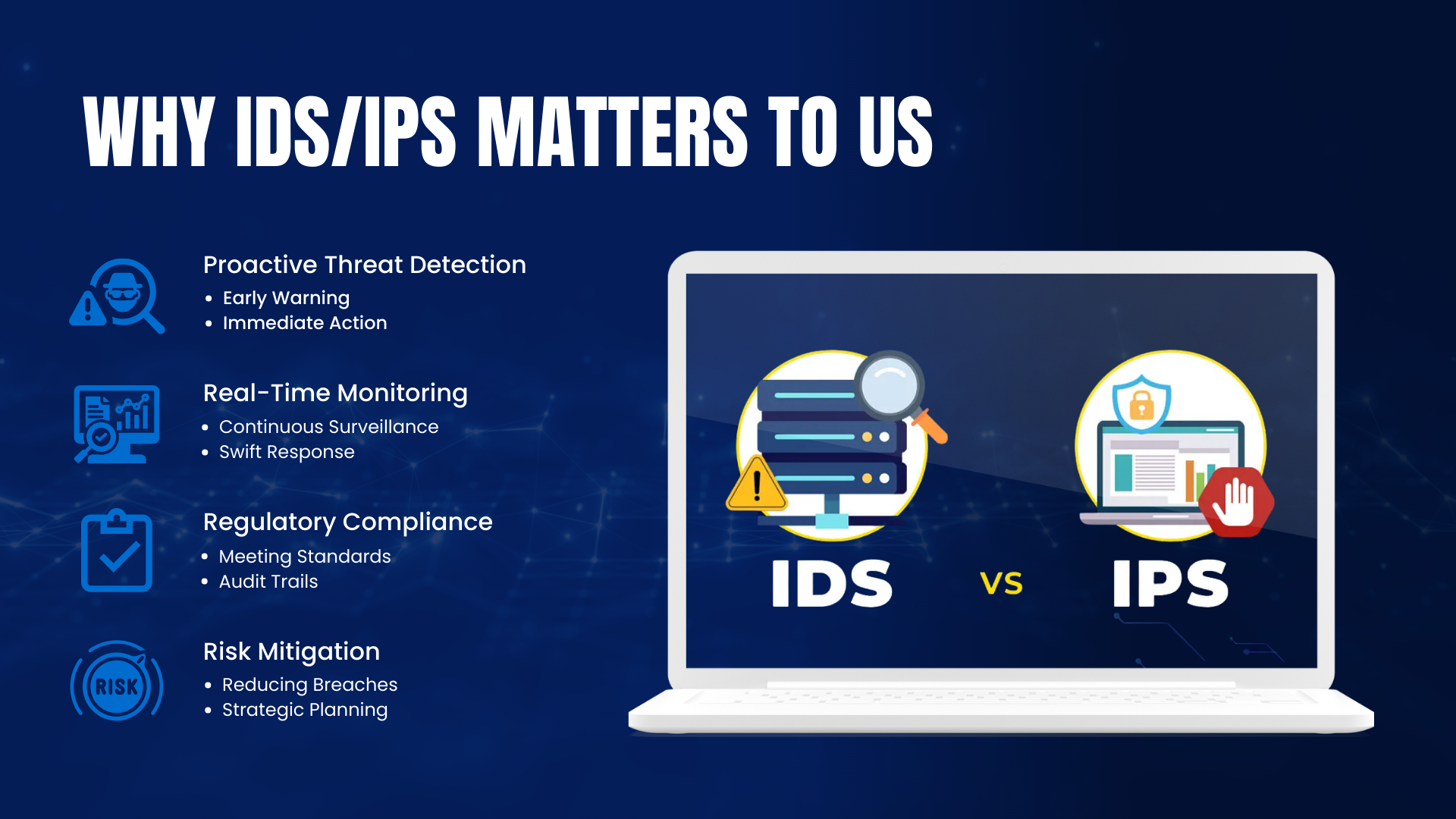
Why IDS/IPS Matter to Us
- Proactive Threat Detection
- Early Warning: IDS alerts us to potential security threats before they become serious issues.
- Immediate Action: IPS can block malicious traffic in real-time, preventing attacks.
- Real-Time Monitoring
- Continuous Surveillance: Keeps an eye on network activity around the clock.
- Swift Response: Enables quick action to mitigate threats as they arise.
- Regulatory Compliance
- Meeting Standards: Helps us comply with cybersecurity regulations and industry best practices.
- Audit Trails: Provides detailed logs required for compliance reporting.
- Risk Mitigation
- Reducing Breaches: Helps prevent security incidents that could harm our operations and reputation.
- Strategic Planning: Informs decisions on improving our cybersecurity measures.
Benefits of Implementing IDS/IPS
- Enhanced Security: Strengthens our defenses against cyber attacks.
- Operational Efficiency: Automates threat detection and prevention, reducing manual efforts.
- Stakeholder Confidence: Shows our commitment to security, building trust with clients and partners.
- Cost Savings: Prevents costly security breaches and downtime.
How IDS/IPS Work
- Traffic Monitoring: Continuously scans network traffic for unusual patterns or known threat signatures.
- Analysis: Uses rules and algorithms to detect potential threats based on predefined criteria.
- Alerting (IDS): Sends notifications to the security team when suspicious activity is detected.
- Prevention (IPS): Automatically blocks or quarantines malicious traffic to prevent damage.
IDS/IPS Solutions
- Snort
- Open-Source IDS/IPS: Widely used for real-time traffic analysis and packet logging.
- Customisation: Allows us to tailor rules to our specific network environment.
- Community Support: Extensive community and a large repository of rules for threat detection.
- Suricata
- Open-Source IDS/IPS: Provides robust intrusion detection and prevention capabilities.
- Protocol Detection: Automatically detects and parses various protocols such as HTTP for deeper inspection.
- Integration Capabilities: Easily integrates with other security tools and platforms, enhancing overall security infrastructure.